Fundamentals of Information Security..pdf
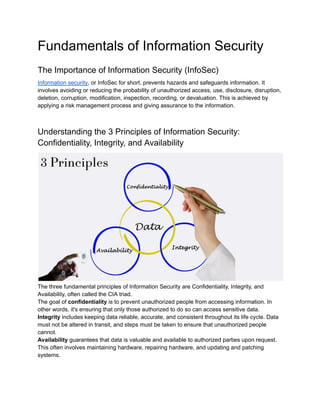
- 1. Fundamentals of Information Security The Importance of Information Security (InfoSec) Information security, or InfoSec for short, prevents hazards and safeguards information. It involves avoiding or reducing the probability of unauthorized access, use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation. This is achieved by applying a risk management process and giving assurance to the information. Understanding the 3 Principles of Information Security: Confidentiality, Integrity, and Availability The three fundamental principles of Information Security are Confidentiality, Integrity, and Availability, often called the CIA triad. The goal of confidentiality is to prevent unauthorized people from accessing information. In other words, it's ensuring that only those authorized to do so can access sensitive data. Integrity includes keeping data reliable, accurate, and consistent throughout its life cycle. Data must not be altered in transit, and steps must be taken to ensure that unauthorized people cannot. Availability guarantees that data is valuable and available to authorized parties upon request. This often involves maintaining hardware, repairing hardware, and updating and patching systems.
- 2. Information Security vs Cybersecurity: Which is More Important? Information Security encompasses a broader scope, focusing on safeguarding all forms of information, physically or digitally. It includes securing sensitive data stored on paper documents, computer systems, or transmitted across networks. Information Security aims to ensure data confidentiality, integrity, and availability, meaning that information is kept confidential from unauthorized access, remains unaltered and trustworthy, and is accessible to authorized users when needed. Cybersecurity, on the other hand, targets explicitly protecting digital assets and systems from cyber threats. It safeguards computers, networks, programs, and data from unauthorized access, cyberattacks, and other digital threats. Cybersecurity focuses on defending against various cyberattacks, such as malware, phishing, ransomware, and denial-of-service (DoS) attacks. Its primary goal is to prevent, detect, and respond to cyber threats targeting digital infrastructure and assets. While Information Security and Cybersecurity share common goals of protecting data and assets, their focus and scope differ. Information Security addresses all forms of information, including physical documents, while Cybersecurity concentrates solely on defending digital assets and systems from cyber threats. Both are crucial components of an organization's overall security posture, with Information Security providing a broader foundation that includes Cybersecurity as a subset. The significance of each ultimately relies on the particular requirements and organizational or situational environment.
- 3. The Role of an Information Security Policy in Protecting Data An Information Security Policy is a set of rules enacted by an organization to ensure that all technology users operate securely and responsibly. These policies are crucial for organizations to protect their systems and data from threats and to comply with legal and regulatory requirements. Understanding the Top Information Security Threats in Today's Digital Landscape Top Information Security threats include malware, phishing, denial-of-service, man-in-the-middle, and SQL injection. These threats exploit vulnerabilities in software and hardware, trick users into revealing sensitive information, or overwhelm systems with traffic to make them unusable. Tools and Techniques Used in Active and Passive Attacks In Information Security, attacks can be categorized as active or passive. Active attacks try to change system resources or interfere with how they function, which may lead to illegal access to or alteration of data. Examples include virus and worm attacks. Passive attacks, on the other hand, aim to intercept and access data traveling over the network without modifying it, such as eavesdropping or data monitoring.
- 4. The Role of Technology in Enforcing Data Protection Laws and Information Security Numerous laws and regulations worldwide deal with Information Security and data protection. These include the California Consumer Privacy Act (CCPA) in the United States, the General Data Protection Regulation (GDPR) in the European Union, and the Personal Data Protection Act (PDPA) in Singapore. These laws aim to protect individual's data and impose strict penalties on organizations that fail to comply with their provisions. Conclusion Information Security, abbreviated as InfoSec, has often been paramount in securing data and digital assets from various threats. By applying the core principles of the CIA, organizations can handle information risks properly and ensure the reliability and availability of their data. With Information Security covering both physical and digital information security, Cybersecurity is that part of cyber security that aims to secure digital assets and systems from cyber threats. While Information Security and Cybersecurity are both fundamental components of an organization's security architecture, Information Security provides the underlying framework that Cybersecurity is a part of. As technology progresses and threats become even more advanced, following the Information Security policies, knowing the main security threats, and using the appropriate tools and techniques are of utmost importance for keeping data secure and in compliance with laws and regulations.