02 a&a all questions
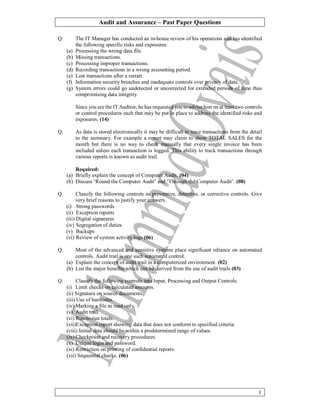
- 1. Audit and Assurance – Past Paper Questions 1 Q. The IT Manager has conducted an in-house review of his operations and has identified the following specific risks and exposures: (a) Processing the wrong data file. (b) Missing transactions. (c) Processing improper transactions. (d) Recording transactions in a wrong accounting period. (e) Lost transactions after a restart. (f) Information security breaches and inadequate controls over privacy of data. (g) System errors could go undetected or uncorrected for extended periods of time thus compromising data integrity. Since you are the IT Auditor, he has requested you to advise him on at least two controls or control procedures each that may be put in place to address the identified risks and exposures. (14) Q. As data is stored electronically it may be difficult to trace transactions from the detail to the summary. For example a report may claim to show TOTAL SALES for the month but there is no way to check manually that every single invoice has been included unless each transaction is logged. This ability to track transactions through various reports is known as audit trail. Required: (a) Briefly explain the concept of Computer Audit. (04) (b) Discuss ‘Round the Computer Audit’ and ‘Through the Computer Audit’. (08) Q. Classify the following controls as preventive, detective, or corrective controls. Give very brief reasons to justify your answers. (i) Strong passwords (ii) Exception reports (iii) Digital signatures (iv) Segregation of duties (v) Backups (vi) Review of system activity logs (06) Q. Most of the advanced and sensitive systems place significant reliance on automated controls. Audit trail is one such automated control. (a) Explain the concept of audit trail in a computerized environment. (02) (b) List the major benefits which can be derived from the use of audit trails (03) Q. Classify the following controls into Input, Processing and Output Controls. (i) Limit checks on calculated amounts. (ii) Signature on source documents. (iii) Use of bar codes. (iv) Marking a file as read only. (v) Audit trail. (vi) Run-to-run totals. (vii)Exception report showing data that does not conform to specified criteria. (viii) Initial data should be within a predetermined range of values. (ix) Checkpoint and recovery procedures. (x) Unique login and password. (xi) Restriction on printing of confidential reports. (xii) Sequential checks. (06)
- 2. Audit and Assurance – Past Paper Questions 2 Q. The internal auditor of Crest Securities Limited has highlighted the following issues in his report: (i) Most of the users have weak passwords. (ii) There is no password expiry policy. (iii) Locked user accounts are unlocked automatically after 24 hours. (iv) Users are allowed to use their smart phones, tablets and laptops for sending and receiving official emails/documents. (v) Firewall is installed with its default policy. Required: Suggest appropriate controls to address the above issues. (10) Q. Segregate the following into preventive, detective and corrective controls and give brief justification in support of your choice. (i) Reviewing credit card bill before payment. (ii) Keeping ATM card PIN separate from ATM card. (iii)Monitoring expenditures against budgeted amounts. (iv) Submitting revised invoices after correction. (v) Updating IT access lists if individual’s role changes. (vi) Review of implemented controls by internal auditor. (vii)Mandatory change of computer passwords after every 45 days. (07) Q. Smart Lease (SL) is a large-sized leasing company, primarily engaged in the leasing of automobiles and industrial equipments. Operations of the company are fully automated and are on custom-built IT applications. Over the last couple of years, the company has experienced a number of IT related security incidents such as sabotage, fraud, and theft of confidential or propriety information, both at head office and in branches. Management has analyzed these incidents and come to the conclusion that majority of these incidents were the work of insiders, i.e. employees of the company itself. Required: Suggest at least six IT security practices/controls which SL should establish to prevent or detect insiders’ attacks on its IT resources. In each case explain the rationale behind your suggestion. (12) Q. Your firm is conducting IT audit of Elegant (Private) Limited (EPL) which is a distributor of FMCG and has a network of branches across the country. Successful implementation of an ERP system in the company last year has led to widespread availability of information in all business areas. Being the job in-charge on this assignment you have decided to adopt ‘concurrent auditing techniques’. However, the audit manager has advised you that since concurrent auditing techniques have never been used previously, the change should be communicated to the client before implementing the same. Required: Prepare a note for EPL’s management describing briefly the factors which have necessitated the use of concurrent auditing techniques; and (07) Q. You are employed in a firm of chartered accountants. This is your second year as the audit supervisor on the audit of Greet Bank Limited. The bank has made considerable progress during the year under review which includes introduction of online banking and increase in the number of branches.
- 3. Audit and Assurance – Past Paper Questions 3 This year you intend to adopt “through the computer” approach as against “around the computer” approach followed last year. Required: (a) Justify the audit approach adopted last year and explain the reasons for the change in approach for the current year. (08) (b) Identify the difficulties which may arise while using “through the computer” approach.(02) Q. Generalized Audit Software provides a means to gain access to and manipulate data maintained on computer storage media. Required: (a) Briefly explain the following functional capabilities provided by the generalized audit software and in each case give two examples of how the auditor might use these functional capabilities: Stratification and frequency analysis Arithmetical Statistical (7.5) (b) Discuss any two limitations of generalized audit software. (03) Q. (a) Identify any six factors that need to be considered while making a decision as regards the use of Computer Assisted Audit Techniques (CAATs). (06) (b) Describe the steps that need to be taken while planning the use of CAATs. (07) Q. Identify the important matters which an IS Auditor would consider while selecting a Computer Assisted Audit Technique. How could greater productivity and improved quality of audits be achieved through CAATs? (06) Q. With the emergence of business conglomerates and globalization the conventional techniques of manual auditing are no longer an option. The quantum, location and complexity of data stored in computerized systems warrants auditing through computer based tools and techniques to ensure efficiency and provide desired level of assurance to the stakeholders. Required: (a) Describe Generalized Audit Software and its major functions. (08) (b) List any four limitations of Generalized Audit Software. (04) Q. Compare the two techniques of auditing in the computerized environment viz. ‘Auditing around the computer’ and ‘Auditing through the computer’ and discuss risks involved, benefit, reliability and ease of implementation. (05)
