Threat Intelligence Keys
•
0 likes•105 views
Type of Data Type of Data Collection Methods Type of Threat Intelligence Feeds
Report
Share
Report
Share
Download to read offline
Recommended
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network SecurityHappiest Minds Technologies
More Related Content
Similar to Threat Intelligence Keys
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network SecurityHappiest Minds Technologies
Similar to Threat Intelligence Keys (20)
A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection

A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection
RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx

RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx
Deep Learning based Threat / Intrusion detection system

Deep Learning based Threat / Intrusion detection system
Study on Data Mining Suitability for Intrusion Detection System (IDS)

Study on Data Mining Suitability for Intrusion Detection System (IDS)
Understanding Cyber Threat Intelligence A Guide for Analysts.pdf

Understanding Cyber Threat Intelligence A Guide for Analysts.pdf
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security
A Survey on Various Data Mining Technique in Intrusion Detection System

A Survey on Various Data Mining Technique in Intrusion Detection System
Digital Shadows and the NIST Cyber Security Framework

Digital Shadows and the NIST Cyber Security Framework
User Behavior based Anomaly Detection for Cyber Network Security

User Behavior based Anomaly Detection for Cyber Network Security
information security (Audit mechanism, intrusion detection, password manageme...

information security (Audit mechanism, intrusion detection, password manageme...
Phi 235 social media security users guide presentation

Phi 235 social media security users guide presentation
Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx

Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx
More from SOCRadar Inc
More from SOCRadar Inc (8)
Recently uploaded
Recently uploaded (20)
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
Kalyanpur ) Call Girls in Lucknow Finest Escorts Service 🍸 8923113531 🎰 Avail...

Kalyanpur ) Call Girls in Lucknow Finest Escorts Service 🍸 8923113531 🎰 Avail...
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
Threat Intelligence Keys
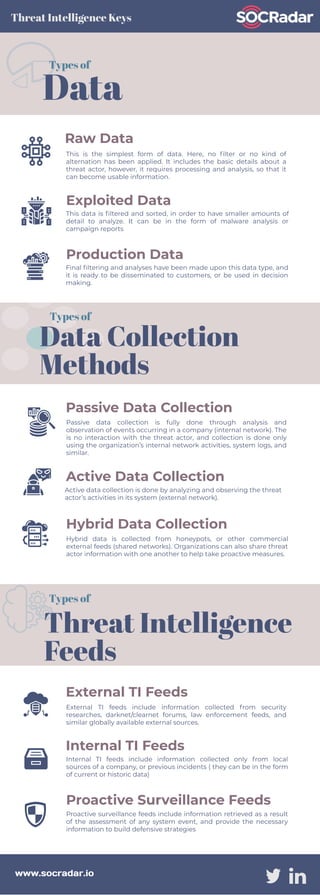
- 1. Raw Data This is the simplest form of data. Here, no filter or no kind of alternation has been applied. It includes the basic details about a threat actor, however, it requires processing and analysis, so that it can become usable information. Exploited Data This data is filtered and sorted, in order to have smaller amounts of detail to analyze. It can be in the form of malware analysis or campaign reports Production Data Final filtering and analyses have been made upon this data type, and it is ready to be disseminated to customers, or be used in decision making. Data Types of Threat Intelligence Keys Passive Data Collection Passive data collection is fully done through analysis and observation of events occurring in a company (internal network). The is no interaction with the threat actor, and collection is done only using the organization’s internal network activities, system logs, and similar. Active Data Collection Active data collection is done by analyzing and observing the threat actor’s activities in its system (external network). Hybrid Data Collection Hybrid data is collected from honeypots, or other commercial external feeds (shared networks). Organizations can also share threat actor information with one another to help take proactive measures. Data Collection Methods Types of External TI Feeds External TI feeds include information collected from security researches, darknet/clearnet forums, law enforcement feeds, and similar globally available external sources. Internal TI Feeds Internal TI feeds include information collected only from local sources of a company, or previous incidents ( they can be in the form of current or historic data) Proactive Surveillance Feeds Proactive surveillance feeds include information retrieved as a result of the assessment of any system event, and provide the necessary information to build defensive strategies www.socradar.io Types of Threat Intelligence Feeds
